So I have two pcaps and I need to get the length of each connection in them and graph them against the connection start times (so y axis is duration and x axis is time). I also need to find connections that did not end with an ACK after a FIN-ACK. I am new to working with pcaps so I am unsure how to do this. I assume wireshark would be easiest but if tcpdump or some other utility would be better that is fine as well. Can anyone help me with a filter? Thanks asked 28 Mar '15, 07:25 thaweatherman |
2 Answers:
You could use the conversations statistics to create a list of all conversations. It has columns for the relative start and duration, so you could export those statistics to graph something in Excel or any other graphical program. The other problem is finding FINs without a following ACK - this is next to impossible, because you can't filter on packet dependencies. There are some tricks to do this for the session start, but not for the session termination. May I ask why you need to find conversations like this? answered 28 Mar '15, 09:35 Jasper ♦♦ |
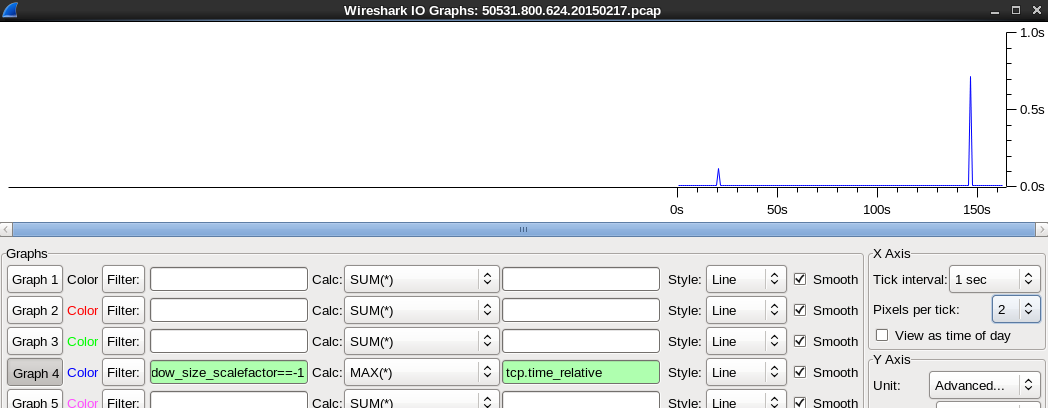
You can filter on all completing TCP connections (SYN->FIN/RST) and use Statistics -> IOGraph to draq the tcp.time_relative on the y axis using y Axis -> Unit advanced. The filter would be For the second part of your question wireshark would have to keep track of the tcp session's state in a variable which you could then filter on tcp.state=="FINWAIT2". It currently doesn't do this but certainly sounds like it could be done - but I'm not a coder so maybe easier said than done ;-) Regards Matthias answered 28 Mar '15, 23:20 mrEEde |

Thanks for your answer. How do I pull up the conversations statistics? It looks like there should be a Conversations option under the Statistics menu but I don't see one (version 1.12.4). As for the FIN without ACK (to keep it simple), I want to record those conversations' lengths as well by assigning a specific time length.
yes, the conversation statistics are found in the statistics menu, and it is definitely available in 1.12.4. its the third options from the top, called "conversations".