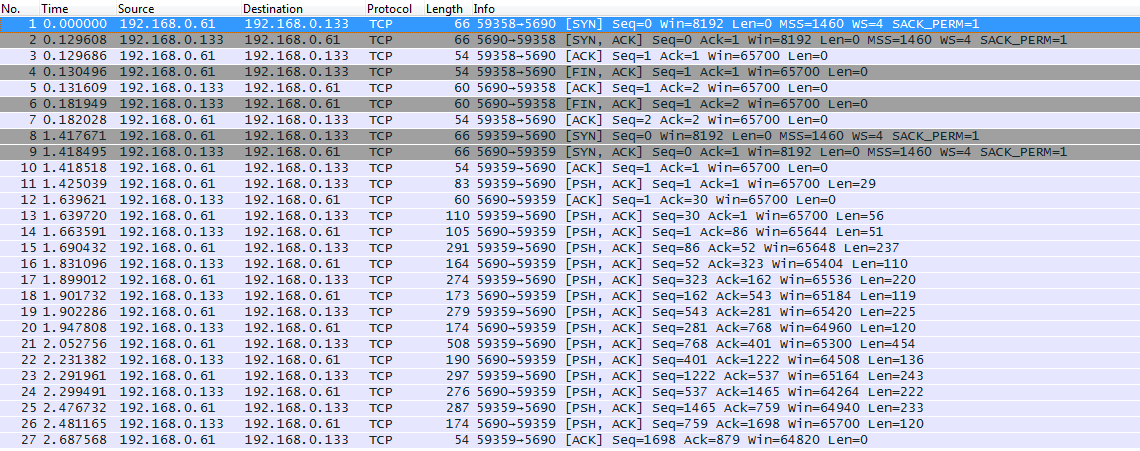
Hello everyone, I captured a tcp traffic using wireshark and saved the traffic in pcap file. I did two tests: For both tests, the TCP replay didn’t work. I’m getting RST. I didn’t find also a traffic comming to my TCP server application. Do you have any ideas on how to resolve this problems? The captured data:
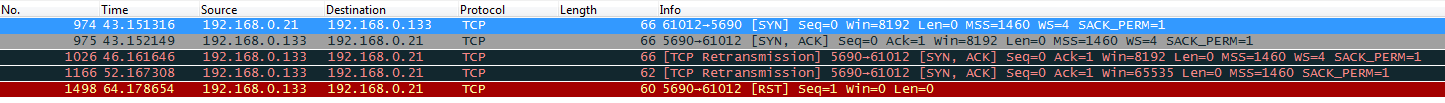
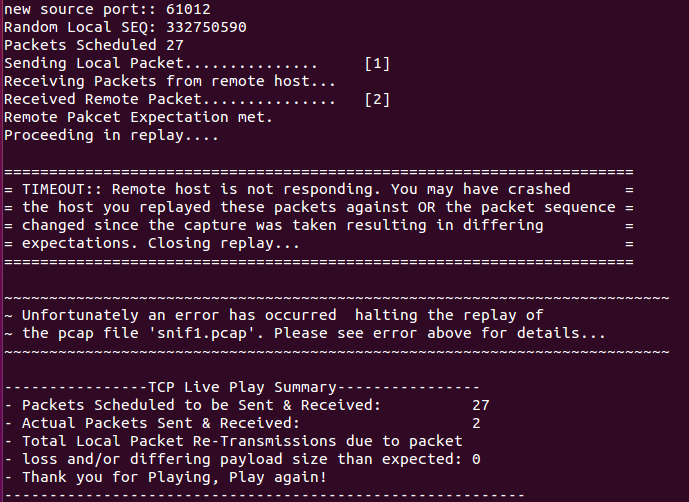
The test results:
Note that I used Kali Linux. Thanks in advance. Jack asked 05 Jan ‘16, 07:42 jackABA 6●1●1●4 edited 06 Jan ‘16, 02:13 |
One Answer:
tcpliveplay description says that it modifies the captured data, while sending them, in such a way that as much as possible of the original packets would be preserved but the tcp session would establish properly, i.e. the SEQ and ACK numbers are not replayed from the stored version but modified to match the initial values of the new session. So little can be said until you make clear at what phase the server sends the RST. After receiving SYN? After receiving the first "real" packet after the initial handshake (SYN, SYN+ACK, ACK)? Both the original capture (which you are attempting to replay) and the capture of the replay attempt would be the best input data for any further analysis. If I've understood you right and the machine which is running the tcpliveplay is getting RST whereas the server has not received even the SYN packet, there is a firewall somewhere on the way between the two machines which prevents the SYN packet from being delivered and itself responds to it with RST. Or you may have missed this part of the manual: Due to the nature of the replay, you must suppress the kernel RST flags because the replay is injecting packets into the replay station’s NIC. Issue the following: Example of suppress command: answered 05 Jan '16, 15:16 sindy edited 05 Jan '16, 15:20 Thanks for quick replay. we have already used the iptables command. but we have the same issue. we are getting RST. I added some screenshots that describe the issue. (06 Jan '16, 02:15) jackABA I agree with @grahamb, but add some more remarks... tcpliveplay says, at the page I've linked in my answer, that the capture to be replayed must contain just a single tcp session. The Wireshark packet list you've pasted from the original capture shows two distinct sessions (packets 1-7 and 8-last), each from a different port at client side. It is possible that this confuses tcpliveplay already before it reaches the end of the first session while sending. So you have to use Wireshark filters and The capture from the replay shows that tcpliveplay has sent the SYN packet, the intended server (or something else) has responded by a SYN,ACK packet, but tcpliveplay has never sent the ACK to that one itself, which made the server make two retransmit attempts for the SYN, ACK, and only after still getting no response, send the RST. (06 Jan '16, 03:15) sindy |

Seems to me this is a tcpreplay issue not Wireshark. You’ll probably find more helpful support on the tcpreplay-users mailing list as suggested by the tcpreplay support page.