Hi, How can I verify from wireshark traces if the fragmentation is happening or not when jumbo frames are configured? Any pattern or messages I need to look for? Also how do I troubleshoot the jumbo frames network performance issues? Thanks!! asked 02 Apr '15, 09:55 vondutch9 |
2 Answers:
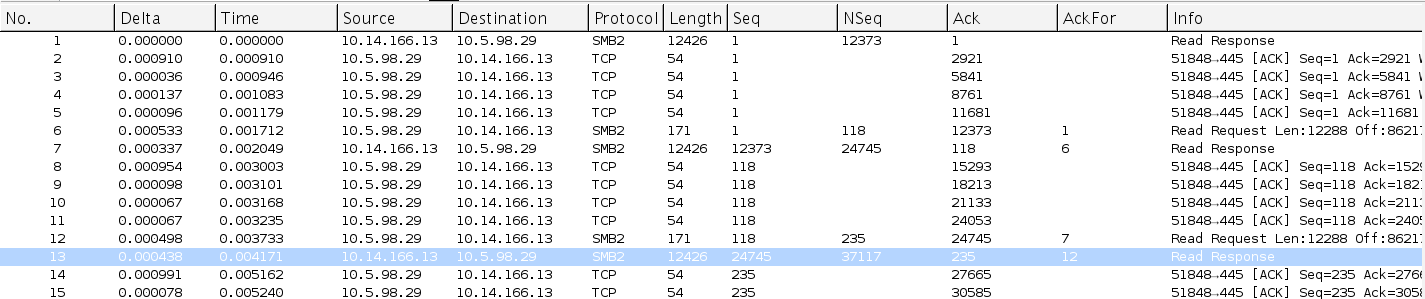
Fragmentation has occured when either the more fragment bit is set or the fragmentation offset is greater than zero. The filter tp display both types would look like: I typically also want to see the packets that require fragmentation but did not allow to be fragmented. So the path MTU discovery process kicks in an reduces the MTU size. A filter on those packet would be icmp.code == 4 So the combination of both in i little more cryptic notation is ip[6:2]&3fff or icmp[1]==4 Regards Matthias answered 02 Apr '15, 12:22 mrEEde edited 03 Apr '15, 01:35 Ok here is what my wireshark trace looks like. Source 10.14.166.13 is sending a packet of size 12426 to destination 10.5.98.29 and then the destination is sending 5 acknowledgements. Each ack packet is a naked acknowledgement and acknowledges 2920 bytes. So can I conclude the packet from 10.14.166.13 is broken down into packets of size 2920 by some router on the way and then delivered to 10.5.98.29? Full size image if gets cropped in your browser, at https://osqa-ask.wireshark.org/upfiles/Screen_Shot_2015-04-03_at_4.28.57_AM.png if the image
(02 Apr '15, 13:38) vondutch9 1 TCP usually acks every 2nd packet so when you see 2920 bytes being acked this means the remote side received two segments of 1460 bytes indicating an MTU size of 1500 along the route. Sending a packet size of 12426 is not possible as even jumboframes only allows an MTU of 9000 bytes. What you see is a trace at the sender that has LArgeSend or Segmentation Offload enabled where segmentation is done by the ethernet card. (02 Apr '15, 14:08) mrEEde So can we conclude that jumbo frames are not being used here at all? How can I make jumbo frames work here? Also if segmentation offload is enabled on nic card then how can wireshark know what size packets are being sent over on the wire? (02 Apr '15, 14:14) vondutch9 1 The easiest way to determine if jumbo frames are used would be to inspect the SYN packets and look at the offered MSS. If you don't have the 3-way handshake you would need to have a trace at the receiver also and see how large the biggest inbound packet is. (02 Apr '15, 20:35) mrEEde 1 "How can I make jumbo frames work here" - well, you need to use an MTU size of 9000 all the way along the path and your network hardware needs to enable it also. So it depends what the 'here' is. http://lmgtfy.com/?q=how+to+enable+jumbo+frames This is drifting away from the original question "how-to-check-if-fragmentation-is-happening" though ;-) (02 Apr '15, 20:46) mrEEde Hi meEEde! Very much appreciate it! Yup, it (02 Apr '15, 22:59) vondutch9 Good to hear, once you consider a question answered please use the checkmark next to the answer to close it out. Thanks (02 Apr '15, 23:38) mrEEde Enabling jumbo frames requires three things:
(03 Apr '15, 02:00) Jasper ♦♦ showing 5 of 8 show 3 more comments |
Please use the following display filter:
You can test it with the following sample capture file
Regards answered 02 Apr '15, 10:03 Kurt Knochner ♦ Thanks for your response. I do see a message Fragmented IP Protocol but when I try to apply the above mentioned filter, it doesn (02 Apr '15, 10:55) vondutch9 TCP never fragments, unless someone cheats. (02 Apr '15, 11:51) Jasper ♦♦
It's a demonstration of an attack. (06 Apr '15, 04:04) Kurt Knochner ♦ |

"How do I troubleshoot the jumbo frames network performance issues?" Start looking at the TCP flows, if you need help open a new thread stating this and provide a capture from both ends of the connection.