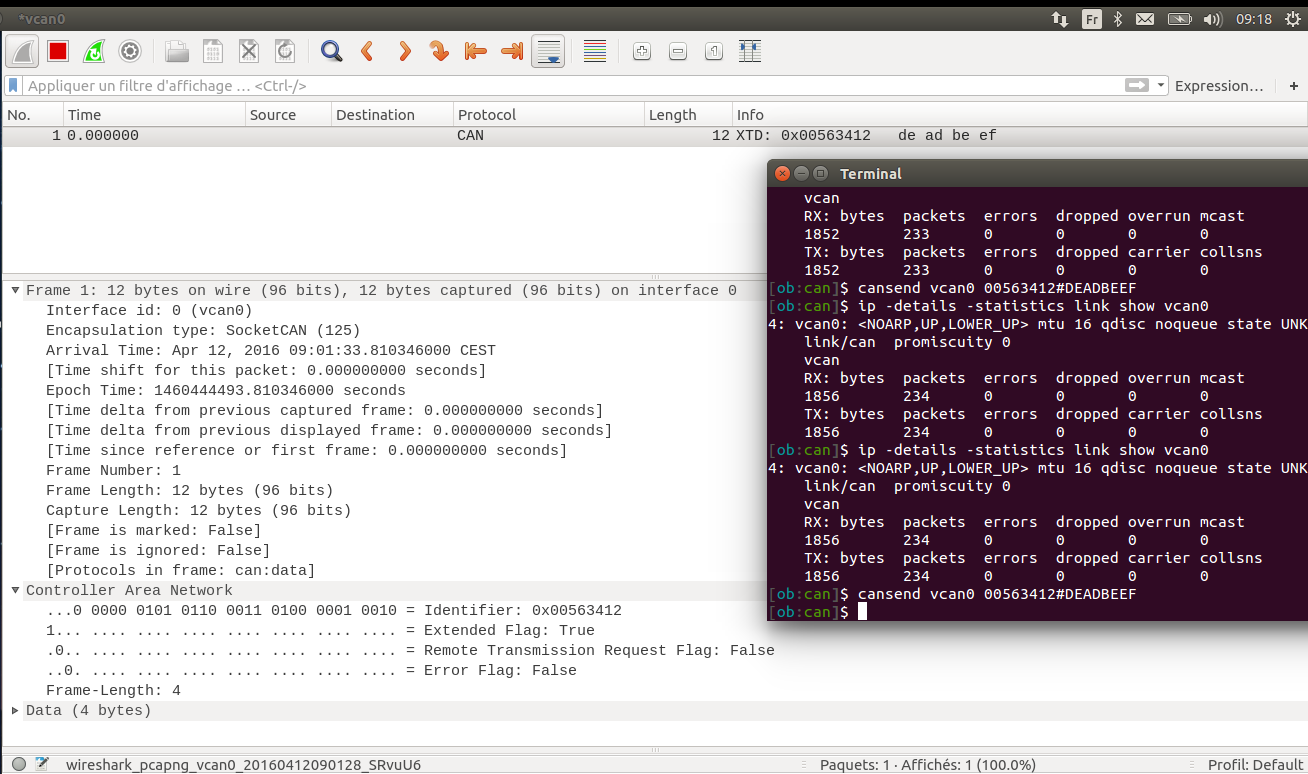
Hi evb, All is in the topic : I'm trying to filter my CAN frames with j1939, but apparently the usage on wireshark is incorrect. I suppose the frame No.1 should be still visible if I type "j1939" (or maybe I should precise the extended ID like "j1939.can_id == 0xdeadbeef") on the textbar... You have to know there is nothing responding on my network, I don't know if this is problematic. I just using can-utils "cansend" command and watching if it still appears below. (see screenshots at the end of this post) Any advice? I don't know how to proceed... Thank you in advance. Cheers asked 12 Apr '16, 00:38 lamoule74 |
One Answer:
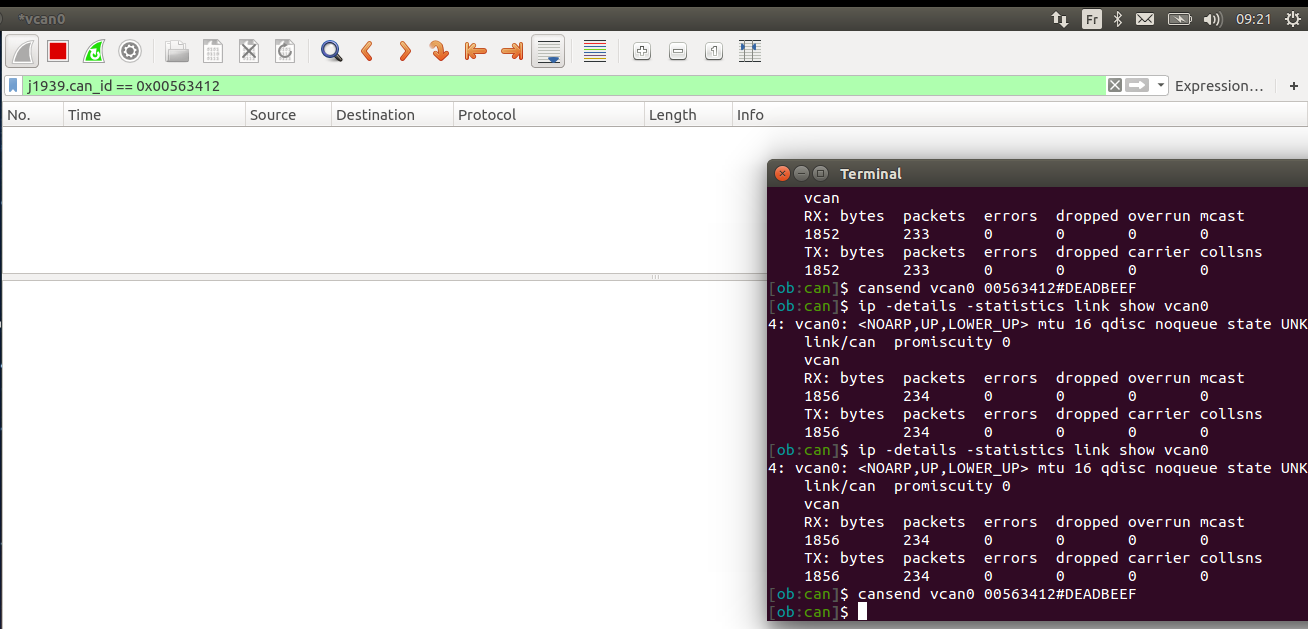
j1939 is a sub-dissector of can, and as can be seen, both from the protocol column and the packet details you have a can frame, so the filter would be The easy way to find any filter name is to select the field in question in the packet details pane and then look at the status bar at the bottom which shows the field info. You can also right click any field in the packet details pane and choose "Apply as Filter" or "Prepare a Filter" to have a filter applied or added with the contents of the field you selected. answered 12 Apr '16, 01:36 grahamb ♦ Hello Grahamb and thanks for replying. OK, I don't really make the difference between "Apply as Filter" or "Prepare a Filter". That's funny because you didn't really give me the solution because I was trying to put a filter only on the protocol, like through the menu : right click on the frame -> decode as -> then in the field you have to save with the current field. Then "J1939" appears in the column protocol. Btw, do you know what "value" field is corresponding to in the decode as windows setting? A mask maybe ?... (12 Apr '16, 02:24) lamoule74 1 Your top screenshot clearly shows the protocol as CAN, both in the protocol column and in the packet details. Maybe redo the screenshot with the CAN identifier selected so that the status bar shows the field info. "Decode as", as a manual setting to decode traffic on some transport layer as something other than Wireshark is currently decoding. This may be necessary because there is insufficient distinguishing material in a protocol to automatically decode it. In the case of CAN there is no unique identifier to determine the subdissector, so "Decode As ..." must be used. Wireshark can be asked to decode CAN traffic as j1939 using the right click "Decode As ...". menu on any CAN frame in the packet list and in the dialog column "Current", select "J1939". (12 Apr '16, 02:50) grahamb ♦ 1
(12 Apr '16, 03:43) sindy Hey sindy,
2.yes, it works! so everything is good for my application now. I understood what I asked initially, so now I just want to know this, go to: right click on any frame -> decode as... -> column Value (I guess because I've got the Fr version) What is it ?? what is the usefulness of this cell ? is that a mask ?.. (12 Apr '16, 05:20) lamoule74 The Value, or Valeur, column is for those protocols that do have a unique identifier field to identify sub-protocols, and allows you to set the value for the corresponding sub-protocol. (12 Apr '16, 05:33) grahamb ♦ I'd make @grahamb's answer more extended: some protocol dissectors decide which other dissectors to invoke for dissecting their payload using dissection tables. The most clear (and probably not realistic because the TCP dissector actually uses a lot of heuristic) example would be a TCP's dissector table where TCP port is used as index: For most cases, Wireshark already knows the default assignment of such values, so "decode as" is only necessary when a non-standard assignment is used in a particular capture, or when no standard assignment exists at all. As there seems to be no "payload type" field in the CAN header, there is no way to use such non-existent value as an index into dissector table, so "Decode as" telling Wireshark that the CAN packets should be interpreted as j1939 must be done manually, and I suppose that the "Value" field is ignored in this case (the authoritative answer is in the source code). So if all your CAN captures are j1939 ones, this static setting of "Decode as" is all you need; otherwise, you may think of creating several Wireshark profiles with different Decode as settings for CAN (but choosing a profile may need an equal number of clicks as changing the Decode as setting). (12 Apr '16, 06:21) sindy OK, gotcha, thank you. (12 Apr '16, 06:42) lamoule74 showing 5 of 7 show 2 more comments |

see below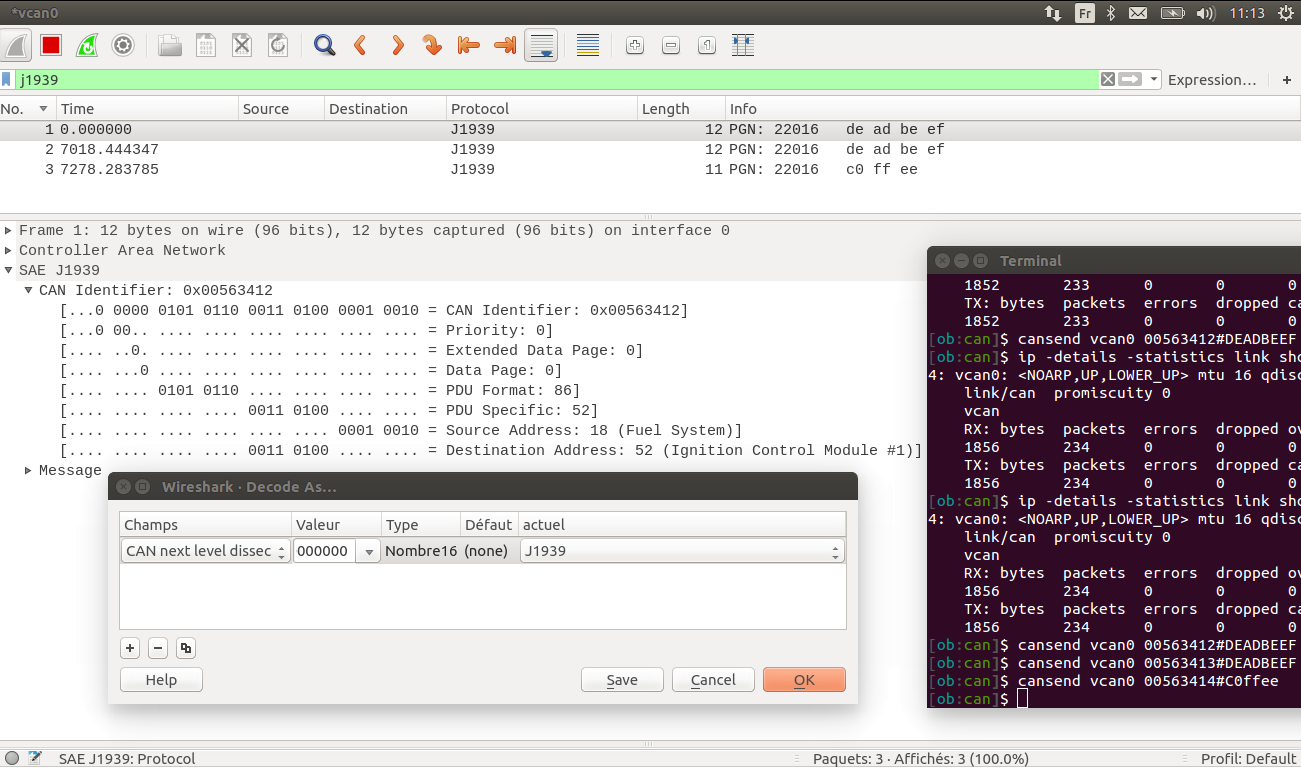
OK, so you now have it dissected as J1939, what is your question?