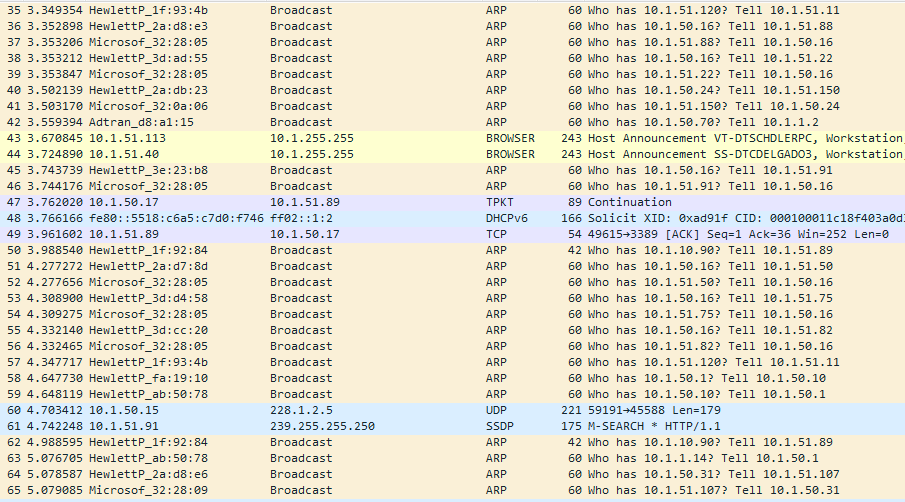
I am trying to find the devices that are asking for ARP how do I find these? the picture below show what I am talking about. Thanks in advance!
asked 28 Sep '16, 06:53 putmantx edited 28 Sep '16, 07:12 |
One Answer:
Why do you call that behaviour "offending"? An ARP request must be broadcast to serve its purpose, and 9 ARP requests per second from 8 different sources, as seen on your picture, are nothing unusual or dangerous. In general, if you find a source MAC address in your captures which spams the network with useless arp requests (say, more than 1 request per second per destination IP address, and more than 500 different addresses), the ARP tables of manageable switches should guide you to the port to which the source equipment is connected. If your switches are not managed, hopefully the network is small enough to allow to find the culprit by checking the MAC address of each connected piece of equipment manually. If the network is large and the switches are not manageable, you have no choice but to use an invasive method - split the network into two halves while monitoring on one port, and see whether the source is in the same half as the port on which you monitor. Iterative splitting of the half identified as containing the source into halves should quickly lead you to a single switch to which the source is connected. answered 28 Sep '16, 07:31 sindy showing 5 of 6 show 1 more comments |

Sindy,
thanks for the info but that is the problem like you said
The HewlettP_(Mac Address) is the one that has multiple MAC addresses why would a device do something like that and not from one specific MAC but change the MAC on every request?
Why do you assume they're the same device? All the HP generated ARP requests with different MAC addresses are asking the response to be sent to different IP addresses, so they look like different devices to me.
There's also a few requests for 10.1.50.16 from HP MAC's and a corresponding ARP for the reverse path from that IP using a Microsoft MAC address, maybe a server?
There are several "harmless" scenarios where a single end device (like a network card) uses multiple MAC addresses, but your screenshot fits none of them.
If several wireless networks are hosted on a single wireless interface, each of them may use its own MAC address but they usually differ only in the rightmost bits. If some kind of device teaming is used, the MAC address of the team is usually different from the MAC addresses of the team members as its higher-order bits, which normally identify a manufacturer, are assigned to the teaming protocol. The same applies to multicast addresses.
So if you are sure that there are more HP MAC addresses in your capture than HP-manufactured devices in your network, it makes sense to suspect some unusual activity (which may then be just pretending that it comes from an HP-manufactured device), and you have to track each of those MAC addresses to the source, using the methods suggested in my answer.
The ARP table of a switch may show that several MAC addresses are associated to a single port. This is normal if the equipment connected to that port is another switch or hub; if it is an end equipment, it deserves investigation.
As far as I can see at the screenshot the hp device does not change the mac every time. Behind the word tell is the up address which want to initiates the ARP request. So I can see different IP addresses.
I cannot see what conclusion regarding normal or malicious behaviour can be made based on how many IP addresses are related to a single MAC address. Multiple IP addresses, even in the same subnet, may be assigned to a single interface.
Several different source MAC addresses bound to a single source IP address would be weird, yes, but that's not what the screenshot shows.
So if a single piece of equipment is spoofing several source MAC addresses, it is quite logical that it is spoofing also the IP addresses associated to them.
I have not seen @grahamb comment. But I mean the same like @grahamb.
Furthermore the screenshot looks calm to me. If it is really malicious than it would be a really impressive spoofing, to me.